Before I start this article, I want to acknowledge and thank one of my blog readers for reaching out to me. On Tuesday, I received an email to my inbox with some kind words and a gentle reminder that this series was left unfinished. That kind of communication is significant to me on so many different levels because most days, I am unsure if these articles are reaching out to the folks that can use them. At any rate, thank you Patrick B for reaching out to me and giving me the motivation I needed to finish up this series!
In this final installment of the BYOD Guest Portal series, I am going to detail how to configure the FortiGate wireless controller to automatically pass the MAC address of the wireless device to the FortiAuthenticator and subsequently allow access based on this information.
Important Caveats
In the previous post of this series, I explained the use case for this particular feature. It is requested as a convenience to the user base because often times, users do not want to have to authenticate to a captive portal each time they bring their device back on to the network. However, it is important to know the implications of turning on this feature.
Enabling this feature can allow for unauthorized access to the network due to the MAC address of devices being easily spoofed with utilities that are built into operating systems today. Also, this feature may be rendered obsolete with the introduction of “randomized MAC addresses” that many mobile devices create when joining a wireless network.
That being said, since this is a “guest” network, the administrator should take proper precautions to ensure that devices that join this network do not have access to any internal or protected services without further validated and authorized connection methods (such as a VPN or ZTNA). In general, the “guest” network is used to allow access to the Internet and nowhere else.
Configure the FortiGate for MAC Authorization
In order for the FortiGate to authorize a device based on its MAC address, the SSID needs to be configured to support mac authorization bypass. This can be done by enabling the “mac-auth-bypass” under the SSID using the example CLI below:
config wireless-controller vap
edit "guest_WIFI"
set mac-auth-bypass enable
next
endOnce this has been completed, the device must be registered in the FortiAuthenticator so that subsequent authorization attempts from that device will be allowed from the FortiGate.
Registering the Device in the FortiAuthenticator
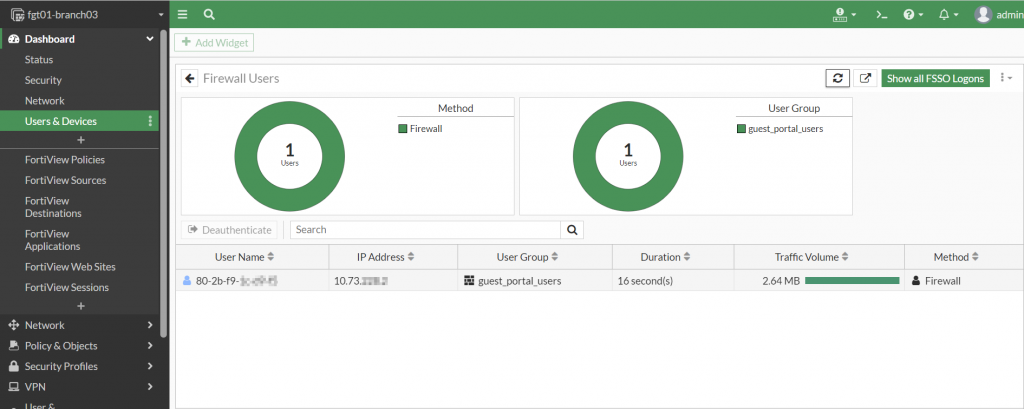
Since the FortiAuthenticator has been configured for device tracking, when a guest user logs in with their registered account, they will be prompted to acknowledge the device with the name and MAC address that will be recorded as part of the user’s devices.
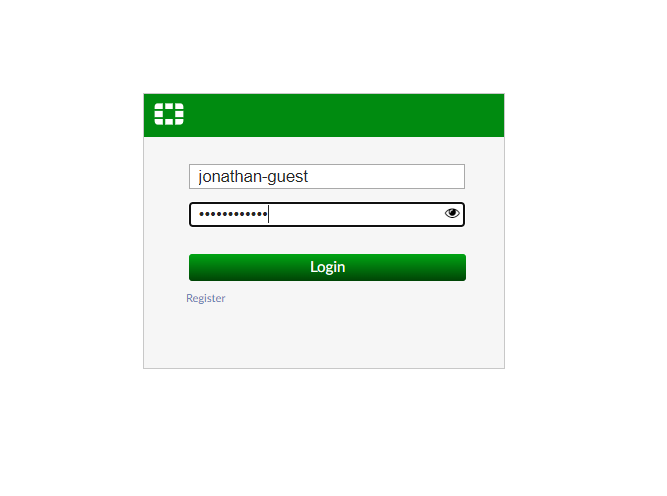
Once the device has been registered by clicking “OK”, the user should be redirected to their original destination.
Validating the Access
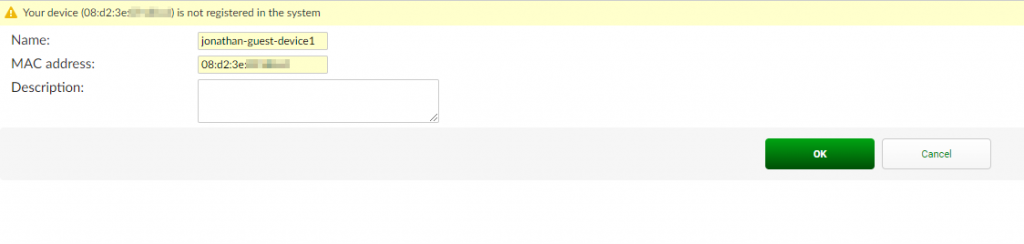
Upon the initial logon with the registered device on the FortiGate wireless network, the user will be tracked by their username they successfully authenticated to the portal with. This is viewable from the “Dashboard | Users & Devices | Firewall Users” monitor widget as shown in the screenshot below:
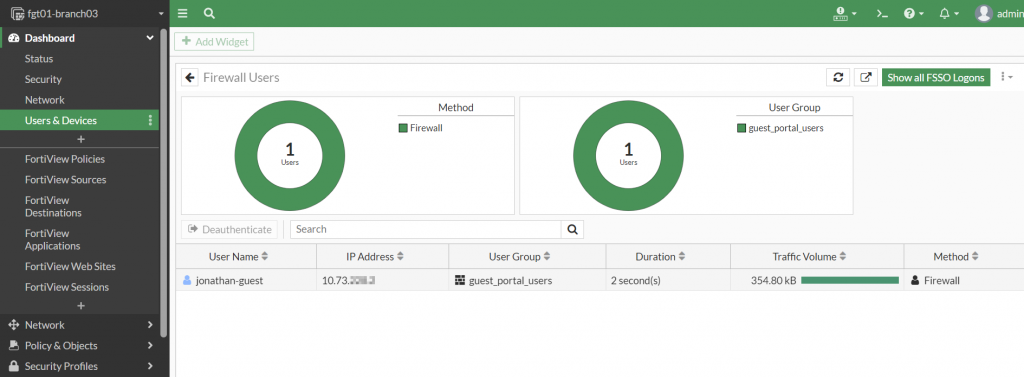
Upon de-authenticating this user and disconnecting and re-connecting the same laptop to the guest WiFi SSID, we observe that the subsequent username maps to the MAC address of the laptop as shown in the screenshot below:
Please note: During this subsequent authentication, the user was not prompted by the captive portal and was immediately granted access to the original web request.
Confirming Devices in FortiAuthenticator
The FortiAuthenticator administrator has the ability to view the devices that are registered to a user. These devices are available under the “Authentication | User Management | MAC Devices” section.
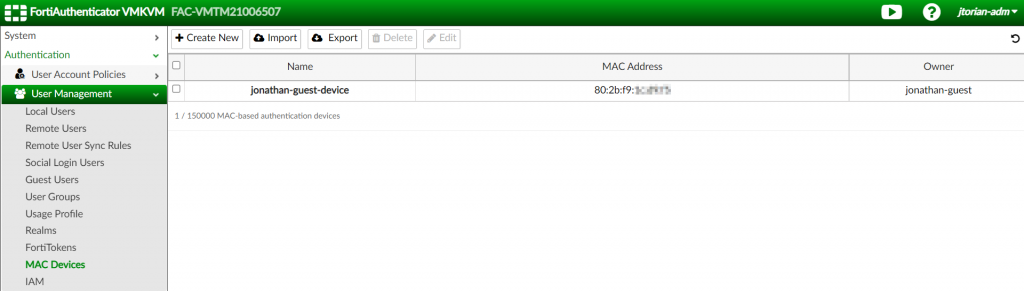
As devices are registered to the FortiAuthenticator, this list will grow dynamically. Also, the user should be able to manage their own registered devices by signing into the captive portal.
To conclude, this is a very useful feature to provide your user base the convenience of not being prompted by a captive portal each time they want to access a guest network with the same device. However, the administrator of the environment needs to take special precautions to ensure enabling this feature does not expose them to unnecessary risk. I hope this series was informative and as always, I hope this helps!
What did you think of this series? Please leave your comments and your feedback below.
